Home > Using File Exchange. What to consider!
Categories: Technical Options
(Last Updated On: )
About This Article
The purpose of this article is to provide a comprehensive overview of how to configure file exchange.
If you want to read about how to configure the “File Exchange” feature, you can do so by clicking here.
A few things to keep in mind when you use “File Exchange” are that:
- File Exchange is available via the Conversations Hub.
- The maximum file upload size is capped at 32 MB.
When you activate the feature, the first sub-option is by default enabled which means that any type of files can be exchanged with the exception of Windows executables (exe, dll, com, bat and msi files), Javascript (js) and script files (sh).
NEW: You can now determine whether agents will need to send a request to the visitor in order for the visitor to upload a file, or whether the visitor will be able to paste the file directly in to the chat.
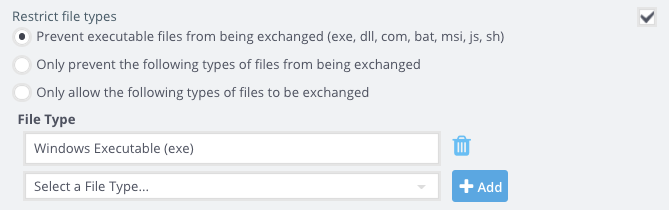
Of course, you have the option to further restrict the types of files that can be exchanged by either adding more restrictions or by only allowing specific types of files.
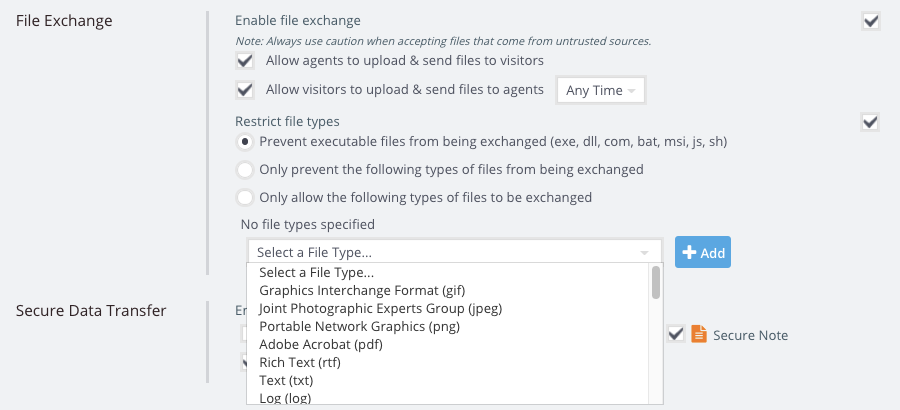
To add a file type restriction, you will need to click on the “+Add” button and select the type of file from the drop-down menu. You can, later remove the restriction by clicking on the trash can icon.
We give you the flexibility to choose what kind of files you want to restrict but our default option was not a random one but rather one trying to ensure the maximum level of security for your organization.
In contrast to other file formats that only display data (eg. jpeg) or play a sound or video (eg. gif), windows executable files have the ability to run an automatic task on your computer. In themselves, executable files are not dangerous but what they contain might be. Any such file contains instructions to your computer which means that if you open and run it, your computer could run operations programmed into that file without asking for your permission.
Script files (sh) are Unix Shell files and are analogous to bat files. It seems to be harder to hide malware in sh files and it is a fact that there is less malware out there for Linux than for Windows.
Javascript files (js) can also contain code that downloads and runs other malware. As it seems, such javascript files are doing a “good” job avoiding antivirus software detection.
Like mentioned above, windows executable and the other two types of files are not necessarily damaging or even threatening. There are, of course, cases when you need to run them in order to use trusted software programs which you download from trusted websites. But what if the instructions the file contains are destructive? For example, an executable file could have instructions to delete every single file on your hard drive.
Apparently, the vast majority of your web-visitors and clients would not have any intentions sending you a harmful executable file but Elvis did sing the “Devil in Disguise”. He surely did not have windows executable, script and javascript files in mind but what you should keep in yours when you use the feature is “Better safe than sorry”!!
You can read more about security related issues here.
Published November 10, 2016
